AFL is a very powerful fuzzer, that tries to be smarter than random input generating fuzzers. It’s cool, but needs a bit more baby sitting. I’ve added some support to Suricata to assist AFL.
Here’s how to get started on fuzzing pcaps.
mkdir ~/tmp/fuzz
git clone https://github.com/inliniac/suricata -b dev-afl-v5
cd suricata
git clone https://github.com/OISF/libhtp -b 0.5.x
bash autogen.sh
export CFLAGS="-fsanitize=address"
export AFLDIR=/opt/afl-1.96b/bin/
export CC="${AFLDIR}/afl-gcc"
export CXX="${AFLDIR}/afl-g++"
./configure --disable-shared --sysconfdir=/etc --enable-afl
The configure output should show:
Compiler: /opt/afl-1.96b/bin//afl-gcc (exec name) / gcc (real)
make
# create tmp output dir for suricata
mkdir tmp/
# test the command to be fuzzed
src/suricata --runmode=single -k none -c suricata.yaml -l tmp/ \
-S /dev/null \
-r /opt/afl-1.96b/share/afl/testcases/others/pcap/small_capture.pcap
# start the fuzzer
export AFL_SKIP_CPUFREQ=1
/opt/afl-1.96b/bin/afl-fuzz -t 100000 -m none \
-i /opt/afl-1.96b/share/afl/testcases/others/pcap/ -o aflout -- \
src/suricata --runmode=single -k none -c suricata.yaml -l tmp/ \
-S /dev/null -r @@
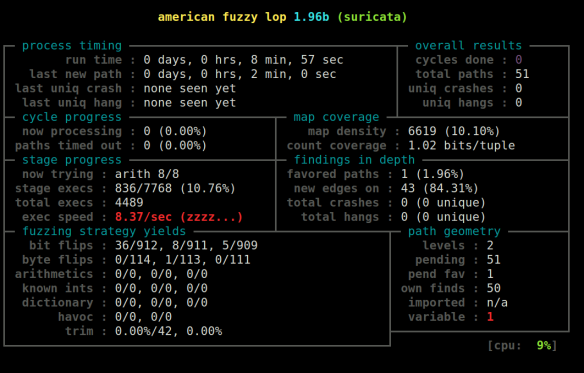
AFL should start running:
Couple of things to keep in mind:
- the above list assumes you have a /etc/suricata/ set up already, including a reference.config and classification.config
- don’t skip the test step or you risk that AFL will just fuzz some basic error reporting by Suricata
- the used ‘dev-afl-v5’ branch makes fuzzing faster and more reliable by disabling random, threading and a few other things
- src/suricata –build-info should show the compiler is afl
- keep your test cases small, even then runtime is going to be very long. AFL takes the input and modifies it to find as many unique code paths as possible
Fuzzing rules and YAMLs
For fuzzing rules and YAMLs the compilation steps are the same.
To fuzz rules, create a directory & test input:
mkdir testrules
echo 'alert http any any -> any any (content:"abc"; sid:1; rev:1;)' \
> testrules/rules.txt
# test command
src/suricata -c suricata.yaml -l tmp/ --afl-parse-rules -T \
-S testrules/rules.txt
# run AFL
export AFL_SKIP_CPUFREQ=1
/opt/afl-1.96b/bin/afl-fuzz -t 100000 -m none \
-i testrules/ -o aflout -- \
src/suricata -c suricata.yaml -l tmp/ --afl-parse-rules \
-T -S @@
Finally, YAMLs:
mkdir testyamls/
cp suricata.yaml testyamls/
# test command
src/suricata -l tmp/ --afl-parse-rules -T -S testrules/rules.txt \
-c testyamls/suricata.yaml
# run AFL
export AFL_SKIP_CPUFREQ=1
/opt/afl-1.96b/bin/afl-fuzz -t 100000 -m none \
-i testyamls/ -o aflout -- \
src/suricata -l tmp/ --afl-parse-rules \
-T -S testrules/rules.txt -c @@
Note that the default YAML is HUGE for this purpose. It may be more efficient to use a sub set of it.
I plan to create some wrapper scripts to make things easier in the near future. Meanwhile, if you have crashes to report, please send them my way!

You must be logged in to post a comment.