 Today, almost 2 years after the release of Suricata 2.0, we released 3.0! This new version of Suricata improves performance, scalability, accuracy and general robustness. Next to this, it brings a lot of new features.
Today, almost 2 years after the release of Suricata 2.0, we released 3.0! This new version of Suricata improves performance, scalability, accuracy and general robustness. Next to this, it brings a lot of new features.
New features are too numerous to mention here, but I’d like to highlight a few:
- netmap support: finally a high speed capture method for our FreeBSD friends, IDS and IPS
- multi-tenancy: single instance, multiple detection configs
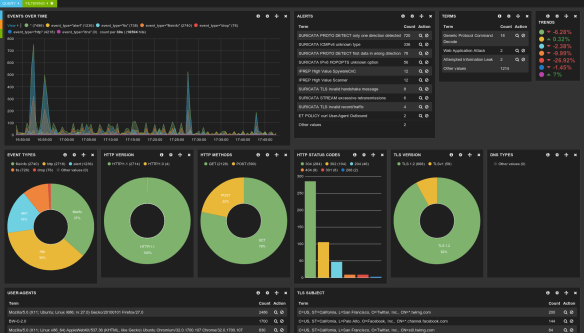
- JSON stats: making it much easier to graph the stats in ELK, etc
- Much improved Lua support: many more fields/protocols available, output scripts
Check the full list here in the announcement: http://suricata-ids.org/2016/01/27/suricata-3-0-available/
New release model
As explained here, this is the first release of the new release model where we’ll be trying for 3 ‘major’ releases a year. We originally hoped for a month of release candidate cycles, but due to some issues found and the holidays + travel on my end it turned into 2 months.
My goal is to optimize our testing and planning to reduce this further, as this release cycle process is effectively an implicit ‘freeze’. Take a look at the number of open pull requests to see what I mean. For the next cycle I’ll also make the freeze explicit, and announce it.
Looking forward
While doing a release is great, my mind is already busy with the next steps. We have a bunch of things coming that are exciting to me.
Performance: my detection engine rewrite work has been tested by many already, and reports are quite positive. I’ve heard reports up to 25% increase, which is a great bonus considering the work was started to clean up this messy code.
ICS/SCADA: Jason Ish is finalizing a DNP3 parser that is very full featured, with detection, logging and lua support. Other protocols are also being developed.
Documentation: we’re in the process of moving our user docs from the wiki to sphinx. This means we’ll have versioned docs, nice pdf exports, etc. It’s already 180 pages!
Plus lots of other things. Keep an eye out on our mailing lists, bug tracker or IRC channel.






You must be logged in to post a comment.